Imagine this:
You’re the Executive Director of a $5 million dollar nonprofit organization. It’s 6:30 AM on Monday morning and even though you wish you were still sleeping; you are logging into your email to follow-up with some donors. You get a login error message, wrong password. You’re still waking up, you probably typed it wrong. You take a sip of coffee and type in your password again. Wrong again. Another sip, another try. OK: now you are SURE you are using the right password. You pick up your phone and as soon as you unlock it you see that you have a bunch of unread text messages. Your phone starts ringing – it’s your trusted and incredibly competent office manager, calling with some bad news: no one can login and it appears you are under attack. Hackers apparently want a specific sum of money to unlock your email accounts. This is a nightmare though you are surely awake.
Your brain starts working and you ask if you can “just call Google and have them reset our accounts or something,” but there’s more bad news: the hackers reveal they have personal information of all your donors and will leak it on the dark web if payment is not made. As the Executive Director, you are being asked: “What’s the plan?”
Was your plan that this wouldn’t happen to your organization?
What is an Incident Response Plan?
In the image below, the “BOOM!” represents the incident itself. It could be any type of cyber incident, including the one we just described, but it could also be a natural disaster like a hurricane or flood, a terrorist attack, a sudden death or absence of key personnel, or any incident that severely impacts your operations. For purposes of THIS article, we are focusing on cyber incidents such as account compromise, data breach, ransomware, and extortion. A company that does not already have a cybersecurity incident response plan (IRP) should strongly consider engaging with a consulting firm who has expertise to develop a detailed plan. A consulting company will ensure that there are no critical omissions that could cause the plan to fail during a real live incident. It is always better to plan and be prepared. Remember, if you are locked out of your system, make sure you can still access your IRP which should be stored out-of-band and accessible during an incident response.
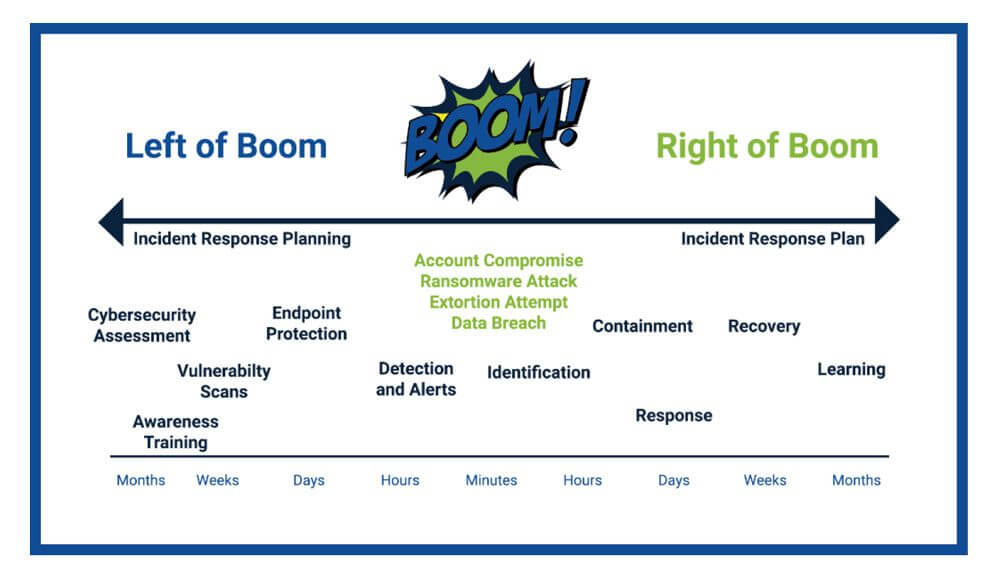
Please note that the items listed left of boom are not meant to be a comprehensive list of protections – there could reasonably be dozens of items listed there – we are just listing a few of the major ones.
Why Do You Want an Incident Response Plan?
Preparing an incident response plan (IRP) accomplishes two primary objectives, both of which have tremendous advantages for your organization:
- In thinking about the types of incidents that may occur and how they will impact you, you will not only be better prepared, but you will identify actions that can reduce the likelihood and severity of those incidents.
- By having an incident response plan in place, you will be able to reduce the impact of an incident when it does occur.
The case for incident response planning becomes a bit clearer if we remove it from our first image:

The Three Most Critical Components of an Incident Response Plan
1.) Declaration
An incident response plan must include guidelines for what constitutes an incident and procedures for declaration.
2.) IR Team and Contact Information
The IRP must include the names and roles of the incident response team along with contact information for ALL the resources that may be needed. This will include technology resources, of course, but also HR, communications, administration, insurance, law enforcement, legal, and any other resource that may be needed in a response.
3.) Procedures
The IRP must include what individual steps should be taken, by whom and in what order. In certain types of incidents (such as data breaches) the consequences of failing to follow a procedure can be very costly. For example, if an overzealous technician wipes a computer that was compromised, they might erase forensic evidence that could be critical in filing an insurance claim.
Phases of Incident Response
The articles linked at the end will each have slightly different phases. Some resources list 4, 5, 6, or more phases. For brevity’s sake, let’s go with four (4) here, but use whatever works best for your organization in your plan.
1.) Declaration:
The declaration phase occurs when an incident is first detected and is determined to satisfy the criteria for invoking the IRP.
2.) Containment:
The containment phase is usually (but not always) performed by technical personnel and involves limiting the impact of the incident as quickly and as safely as possible. It is critically important to follow procedures in this phase to avoid making errors that can increase the liability of the organization and/or destroy forensic evidence.
3.) Response:
The response phase includes all activities involved in responding to and recovering from the incident. Depending on the incident this could include sending out breach notifications, working with incident responders, recovering backups, restoring systems, running scans and tests, and all activities required to restore business operations, constituent confidence, financial stability, and personnel safety.
4.) Learning:
The final phase, once the dust has settled and everyone has had a chance to take a breath, is to gather the response team and review any lessons learned. There’s a famous quote (sometimes attributed to Winston Churchill and at other times Rahm Emanuel): “Never let a crisis go to waste.”
Learning from an incident can be an invaluable experience that can help you be much better prepared in the future. Don’t let it go to waste.
Helpful Resources
There are many good articles and ebooks where you can learn more about incident response planning. Here are 3 that are highly recommended:
1.) (short): Incident Response Plan | Defendify
2.) (medium): 6 Phases in the Incident Response Plan | Security Metrics
3.) (long): The Incident Responder’s Field Guide | Digital Guardian